Law enforcement has started to distribute an Emotet module to infected devices that will uninstall the malware on April 25th, 2021.
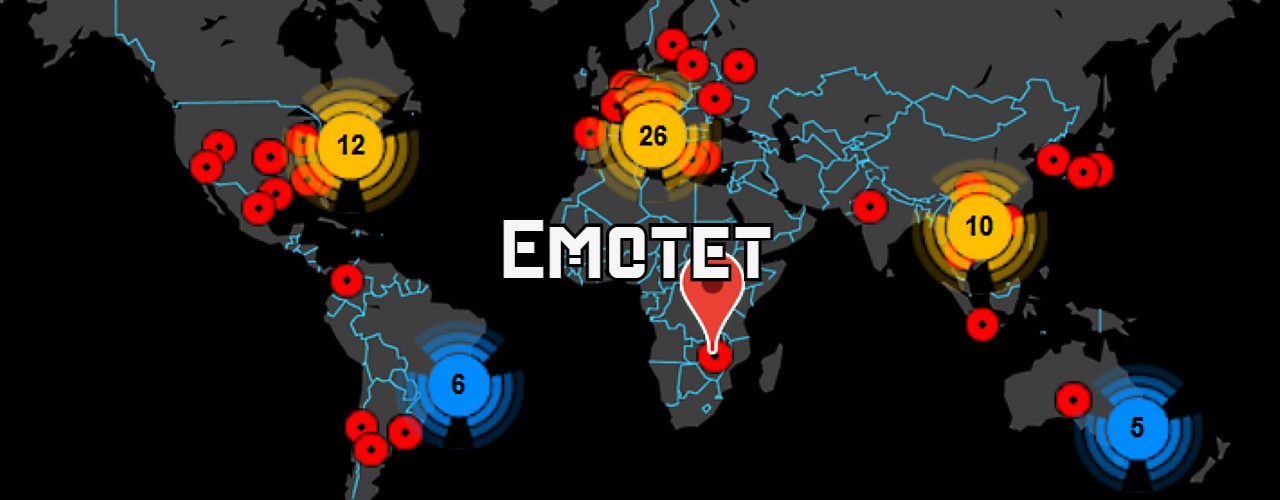
Today, Europol announced the disruption of the infamous Emotet email spamming botnet used to distribute malicious Word spam attachments that install malware such as TrickBot and Qbot.
These attacks usually lead to the full network compromise of infected companies and the deployment of Ryuk and Conti by TrickBot, and ProLock or Egregor by Qbot.
Emotet to be automatically uninstalled on April 25th
After infecting victims, Emotet will distribute various modules to infected devices that perform different malicious activities.
After today's Emotet announcement, a security researcher known as Milkream discovered that Emotet had begun to push down a new module to infected devices.
This module will uninstall the Emotet malware from infected devices on April 25th, 2021, at 12:00 (See update at bottom of article).
According to milkream, Emotet is now using the following command and control server IP, all located in Germany.
80.158.3[.]161:443
80.158.51[.]209:8080
80.158.35[.]51:80
80.158.63[.]78:443
80.158.53[.]167:80
80.158.62[.]194:443
80.158.59[.]174:8080
80.158.43[.]136:80
In a phone call with Europol's press office, BleepingComputer was told that the German Bundeskriminalamt (BKA) federal police agency was responsible for this action. The press office, though, did not know the date that law enforcement would uninstall the malware.
It unknown why law enforcement is waiting two months to uninstall the malware.
In response to our questions about this module, Germany's BKA shared the following statement:
"Within the framework of the criminal procedural measures carried out at international level, the Bundeskriminalamt has arranged for the malware Emotet to be quarantined in the computer systems affected. An identification of the systems affected is necessary in order to seize evidence and to enable the users concerned to carry out a complete system clean-up to prevent further offences. For this purpose, the communication parameters of the software have been adjusted in a way that the victim systems no longer communicate with the infrastructure of the offenders but with an infrastructure created for the seizure of evidence." - German Bundeskriminalamt
A January 28th press release by the Department of Justice further states that foreign law enforcement replaced the C2 servers with their own servers to distribute a "law enforcement file."
"Foreign law enforcement, working in collaboration with the FBI, replaced Emotet malware on servers located in their jurisdiction with a file created by law enforcement, according to the affidavit. This was done with the intent that computers in the United States and elsewhere that were infected by the Emotet malware would download the law enforcement file during an already-programmed Emotet update."
"The law enforcement file prevents the administrators of the Emotet botnet from further communicating with infected computers. The law enforcement file does not remediate other malware that was already installed on the infected computer through Emotet; instead, it is designed to prevent additional malware from being installed on the infected computer by untethering the victim computer from the botnet," states a Department of Justice press release.
With law enforcement taking control over the botnet and now distributing a module that will uninstall it in March, this could be a significant disruption that will make it very difficult for Emotet to return.
With that said, there were hopes that the US governments and Microsoft disruption of TrickBot in October would have had a long term effect, but TrickBot was soon back up and running.
For now, though, security researchers and professionals are excited by this development. This feeling is especially true for Joseph Roosen of the Cryptolaemus research group, who has been tirelessly monitoring and warning the world of Emotet's activities.
"I feel great and very hopeful about the future. The collaboration between law enforcement, private sector and volunteers is a beautiful thing to behold," Roosen told BleepingComputer.
Update 1/28/21 12:24 PM EST: Our article originally stated that this new module uninstalls Emotet on March 25th, 2021. After further analysis by Malwarebytes and other security researchers, the actual uninstall date is April 25th, 2021.
The new module sets tm.tm_mon, which corresponds to the month of a year, to 3. This was originally thought to equal March, with the value of 1 being January.
The Microsoft documentation for the Time structure states that the month value starts at 0 instead, with 0 being January, and thus a value of 3 equaling April.
This means that the uninstall date used by this module is actually April 25th, 2021, at 12:00.
We have also updated the title of this article to reflect the correct date.